5 signs your current chat app is leaking metadata
Many communication tools still expose metadata—information about who communicated, when, how often, and sometimes under what circumstances. Even when message contents are encrypted, those surrounding signals can reveal patterns about behavior, relationships, and routines.
Here are five common signs your chat app may be revealing more than it should—and how Qaxa approaches those same problems differently.
1. Constant presence tracking
That green dot may look harmless, but in many systems it depends on regular presence updates sent to a central service.
What it can reveal
Over time, presence signals can create a pattern of when you are active, when you go offline, and how your working routine looks.
How Qaxa approaches it
Presence should be useful in the moment, not valuable as a long-term behavioral record. Qaxa treats it as a live signal rather than something that should become a durable timeline.
2. Typing indicators that create interaction data
Those three bouncing dots are cute. They’re also data.
What it can reveal
Depending on the system design, typing signals may show how quickly someone responds, how long they hesitate, and when they are most active.
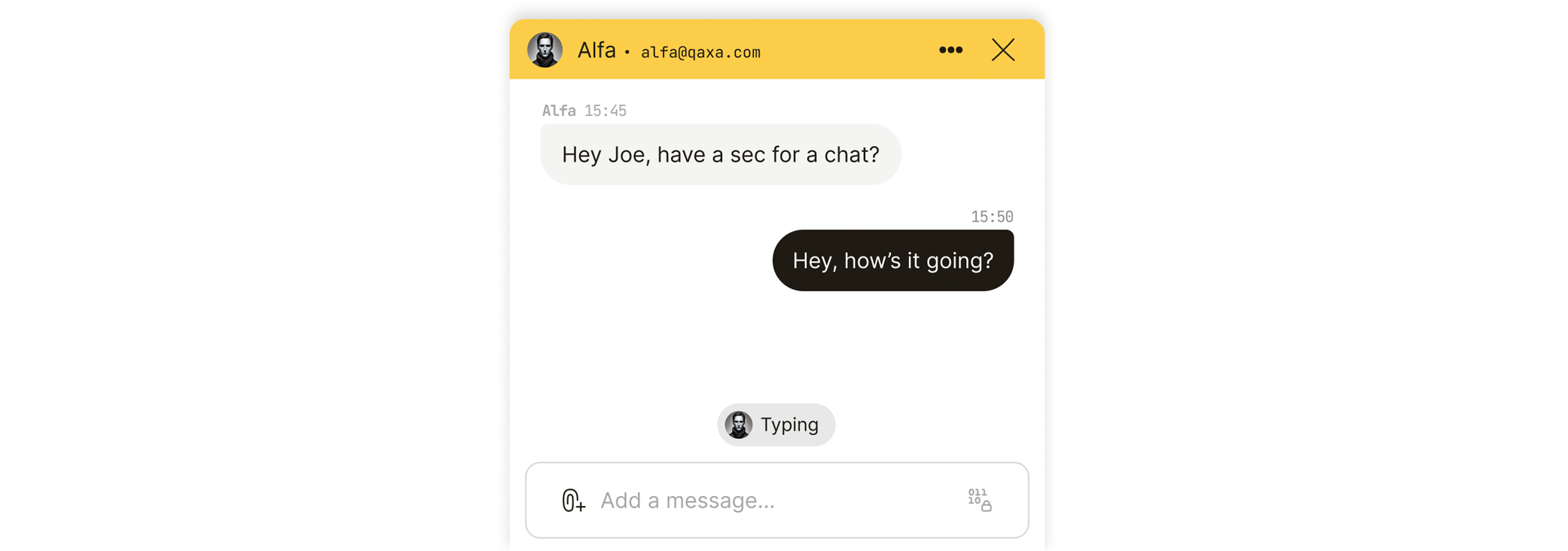
How Qaxa approaches it
Typing is shown only as a live, momentary signal while both participants are active in the conversation. It is not stored as a message event or kept as a historical activity record.
3. Precise read receipts
“Read at 10:04 AM” sounds helpful. It can also be more revealing than necessary.
What it can reveal
Granular read receipts can create a detailed timeline of when a person opened or viewed a specific message.
How Qaxa approaches it
Qaxa keeps this coarser. The goal is to support coordination without turning attention into a fine-grained audit trail.
4. Link previews generated through the provider
Link previews make conversations easier to scan, but they can come with privacy tradeoffs.
What it can reveal
If previews are fetched server-side, the provider may learn what links are being shared. In some cases, the destination site may also see requests generated as part of the preview process.
How Qaxa approaches it
Qaxa does not generate rich link previews. If you paste a link, it stays a link. That avoids the extra fetching and metadata exposure that previews can introduce.
5. Communication models that expose metadata by design
Some systems reveal more metadata simply because of how they are built.
What it can reveal
Traditional email, for example, often leaves sender, recipient, timing, and subject-related metadata more exposed than users expect. That is a useful reminder that content encryption is only one part of privacy.
How Qaxa approaches it
Qaxa is built as a private collaboration environment rather than an email protocol layered over public routing infrastructure. That gives more room to reduce unnecessary metadata exposure at the system level.
Reality check
No system eliminates metadata completely. Networks still reveal that traffic happened. The goal is not perfection. The goal is to avoid collecting, storing, and exposing more than necessary.
Conclusion
A privacy-conscious communication tool should protect more than message contents. It should also be careful about presence, timing, visibility, previews, and other signals that quietly describe how people work.
That is the difference between encrypted messaging and a genuinely metadata-aware system.
—
Now that you’ve seen how metadata leaks happen, it helps to understand the encryption model behind Qaxa. We don’t rely on “trust us” promises—we rely on proven cryptography. Read next: Why Qaxa Uses PGP, and why established encryption standards still matter.



