Your deal is scattered across inboxes, cloud links, and spreadsheets.
Files sit behind links. Questions move through email. Status lives in spreadsheets. Within days, no one can see the whole deal.
Scattered context
Comments on drafts live in email. Questions move to chat. Open items sit in a spreadsheet. Soon, no one can see it all without checking five places.
Uncontrolled access
A sensitive draft sent three months ago may still sit in someone’s inbox. It may have been forwarded. You have no reliable way to take it back.
Exposed by default
Your provider can probably read your files. If they're subpoenaed, they may have to hand them over. Convenience tools weren't built for this.
Onboarding friction
The other side may not adopt a new system just for one deal. If joining feels heavy, both sides fall back to email.
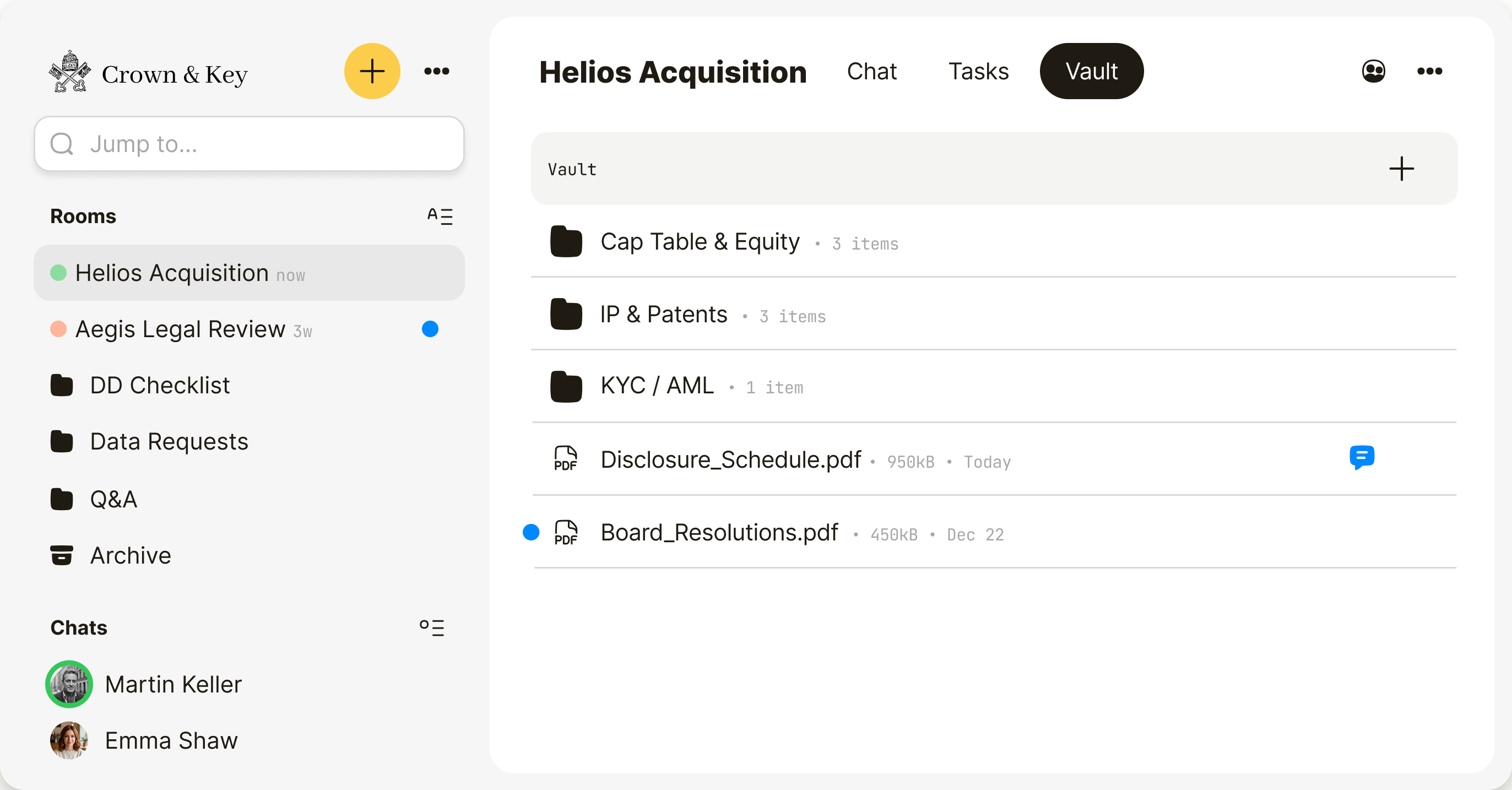
The other side joins in seconds.
On the other side, most tools create friction. Qaxa rooms open in the browser, so counterparties can review files, answer questions, and complete tasks — without IT setup or training.
- No apps to install
- No training required
- Guests always free

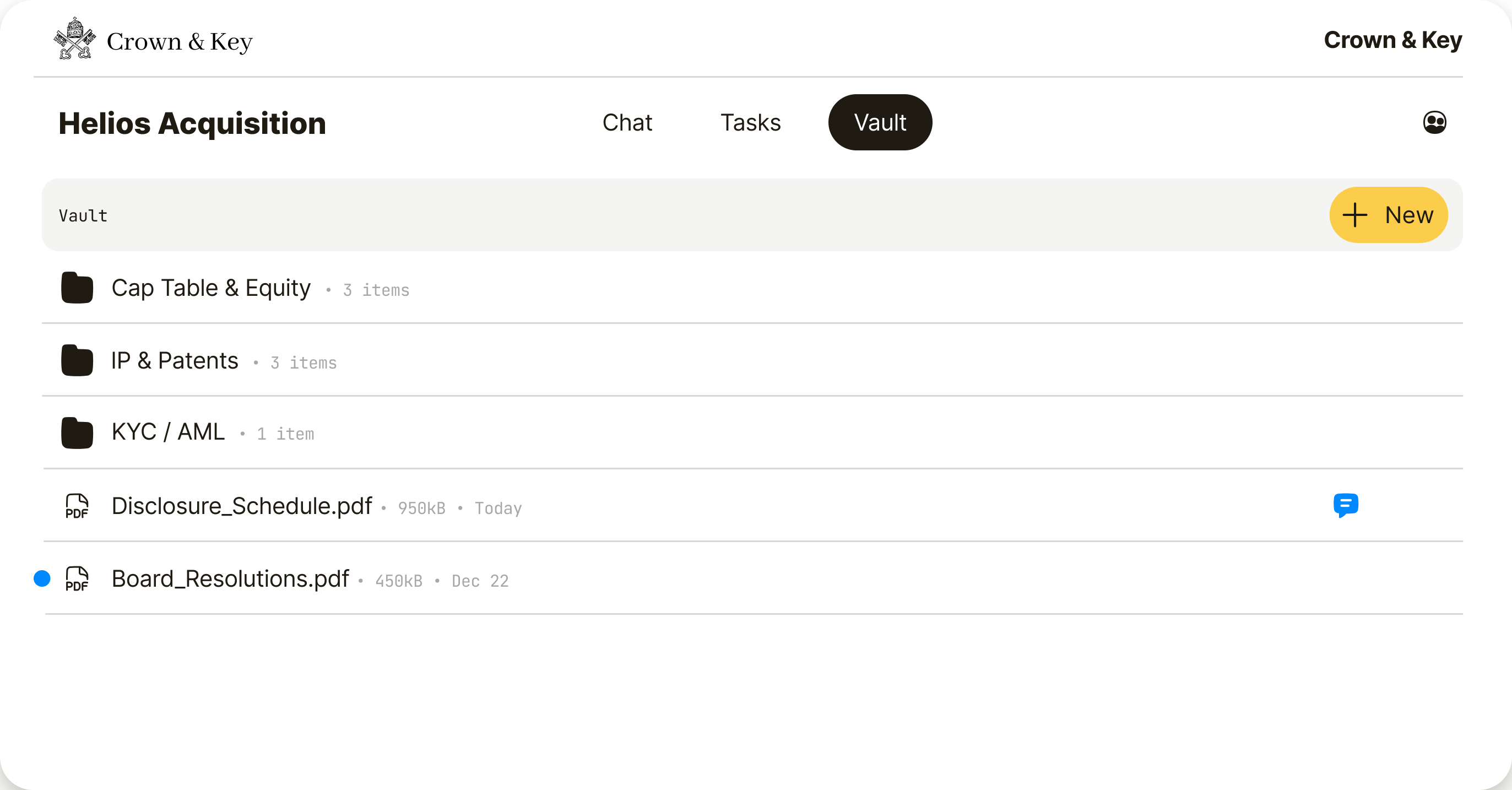
Keep sensitive files out of email.
Email creates copies you can’t revoke. Links get forwarded. Threads get lost. Qaxa keeps files, conversations, and the deal in one encrypted room.
- Files & comments — out of email
- Access controlled from one place
- End-to-end encrypted by default

End-to-end encrypted.
By default.
Qaxa never holds the keys to read your room. Content is encrypted on your device before it reaches our servers — even we can't decrypt it. If we're subpoenaed, we have nothing to hand over.

For the teams moving the deal.
Boutique M&A advisors, transactional law firms, and deal teams use Qaxa to run sensitive transactions in one private room — without files scattered across email, drives, and chat.
Run sell-side and buy-side mandates in private rooms. Bring in counsel and counterparties as free guests. Keep agreements, cap tables, and diligence together — without a VDR for every small deal.
Run M&A, financings, and restructuring matters in private rooms. Bring in counsel, opposing counsel, and clients as free guests. Keep drafts and diligence in one encrypted room — without sensitive material in personal inboxes.
Run buy-side and sell-side deal flow in private rooms. Bring in advisors, counsel, and counterparties as free guests. Keep diligence and discussion together — without enterprise VDR seats you don't need.
“In 2025, breaches involving a third party reached 48% — up 60% in a single year.”